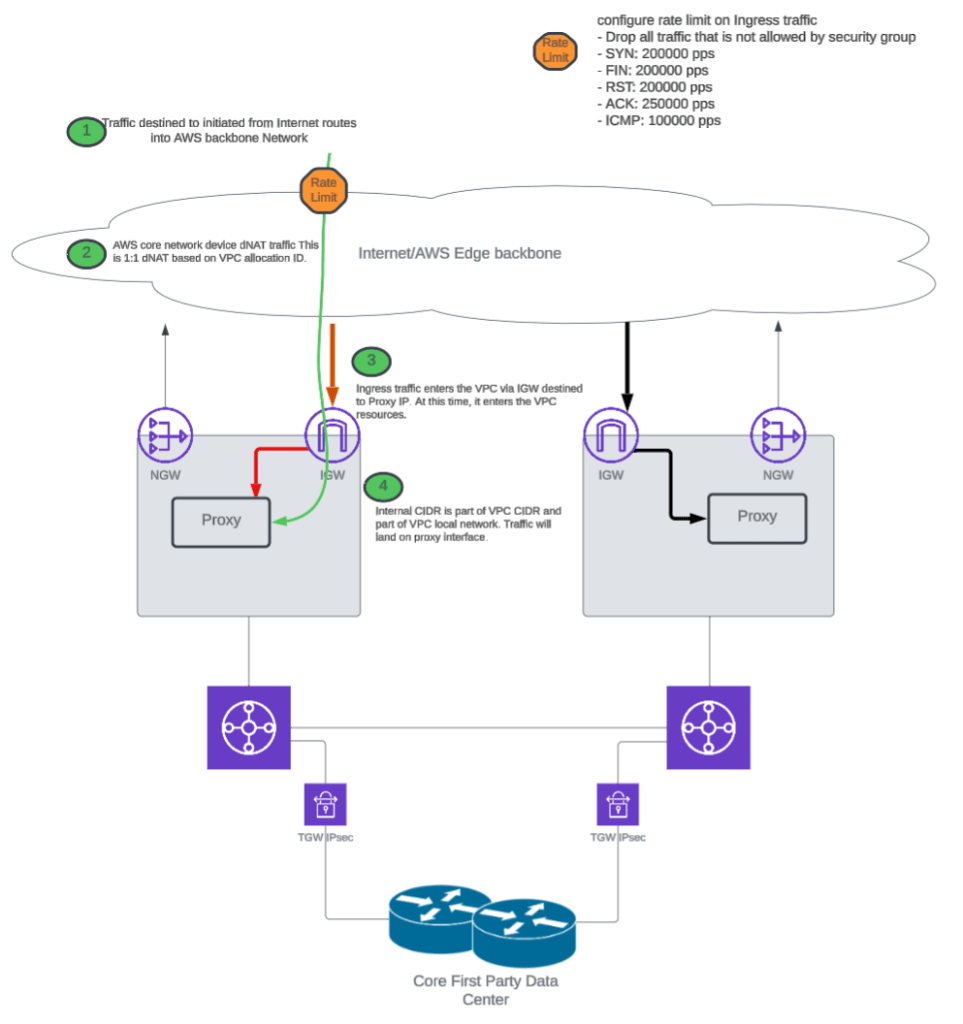
Using two Transit Gateways (TGWs) in a cloud network architecture can introduce certain complexities, especially in terms of routing and security. One of the main challenges pointed out below is that when routes are propagated between two TGWs, it can inadvertently expand the attack surface, especially in the context of DDoS attacks. Here’s a breakdown of the potential mistakes and issues that can arise from using two TGWs in such scenarios:
1. Route Propagation Between TGWs:
- Increased Attack Surface: When TGWs propagate routes to each other, they essentially advertise the full list of routes across both gateways. If the security rules aren’t properly managed, this could expose additional resources to attack vectors. This means an attacker targeting one TGW might get access to other parts of your network through the propagated routes.
- Complex Route Management: Having two TGWs can create challenges in managing and securing routing information. If route propagation is misconfigured, you could inadvertently advertise internal routes to the wrong networks or create routing loops, which could be exploited by attackers.
2. Security Implications:
- Expanded Blast Radius in DDoS Attacks: If one TGW becomes a target of a DDoS attack, the propagated routes could inadvertently allow the traffic to affect additional resources that might be on the other TGW. Since both TGWs are now aware of each other’s routes, the attack vector can grow, leading to a larger blast radius for security events.
- Lack of Segmentation: If two TGWs are used without proper segmentation or isolation between resources, it could create an unintended trust relationship between different parts of your network. In the event of an attack, this lack of segmentation might allow lateral movement from one compromised resource to another, further amplifying the potential damage.
3. Redundancy and Availability:
- Potential Single Point of Failure (SPOF): If the routing between the TGWs isn’t properly designed to handle failover, a failure in one TGW could cause disruption across the entire network. Additionally, if route propagation is bidirectional, failure in one could affect the availability of other network segments.
- Increased Latency and Bottlenecks: When routes are propagated between two TGWs, this could lead to traffic being directed through unintended paths, possibly adding latency or creating bottlenecks. This could be exacerbated during a DDoS attack when traffic volume spikes.
4. Misconfiguration Risks:
- Unintended Exposure of Internal Networks: Misconfigured route propagation or security group settings can result in exposing internal resources to the internet or other parts of the network that were meant to be isolated. In the case of a DDoS attack, this could result in unprotected or under-protected services being overwhelmed.
- Overly Permissive Routing Policies: If there are overly permissive routing rules between the TGWs, they could route traffic from unauthorized or unexpected sources. During an attack, this can amplify the volume of malicious traffic hitting multiple endpoints within your network.
Best Practices to Mitigate These Risks:
- Use Route Filters: Control which routes are propagated between TGWs to limit exposure and ensure only necessary routes are advertised.
- Implement Strong Segmentation: Ensure proper segmentation between different environments or applications within your network to prevent lateral movement of malicious traffic in the event of a breach or DDoS attack.
- Limit Propagation to Specific VPCs: Avoid wide-scale propagation of routes across all VPCs, especially those with sensitive or high-risk assets. Only propagate routes to specific VPCs that need them.
- Deploy DDoS Protection Mechanisms: Utilize DDoS mitigation tools, such as AWS Shield, to protect against volumetric attacks. Additionally, ensure proper rate-limiting and traffic filtering is in place.
- Redundant and Scalable TGW Configuration: Design TGWs in a way that allows for failover and load balancing, ensuring that if one TGW fails, the other can handle the traffic without causing major disruptions.
- Constant Monitoring and Logging: Implement continuous monitoring, logging, and alerting to detect any unusual traffic patterns or configuration changes that could indicate a potential attack or misconfiguration.
By carefully managing route propagation, security segmentation, and redundancy, you can minimize the risks associated with using multiple TGWs and reduce the exposure to potential DDoS attacks or other security incidents.

Leave a comment